Section
Passwords And Authentication
Guides, explainers, and practical reads updated regularly.
All Articles
Techniques for Constructing Strong Passphrases You Can Remember
Why Passphrases Matter in Cybersecurity In the ever-evolving landscape of cybersecurity, passwords have long been the cornerstone of authent…

Understanding When to Use SSO or MFA in Secure Access Scenarios
Balancing Security and Usability: An Introduction to SSO and MFA In the dynamic landscape of cybersecurity, ensuring secure access to system…

Designing User-Friendly Passphrases That Don't Compromise Security
The Evolution of Passwords to Passphrases In the digital age, passwords are a fundamental aspect of cybersecurity, serving as the first line…

Leveraging Role-Based Systems to Enhance Overall Password Security Efforts
Understanding Role-Based Access Control (RBAC) Role-Based Access Control (RBAC) is a critical component of cybersecurity frameworks, particu…

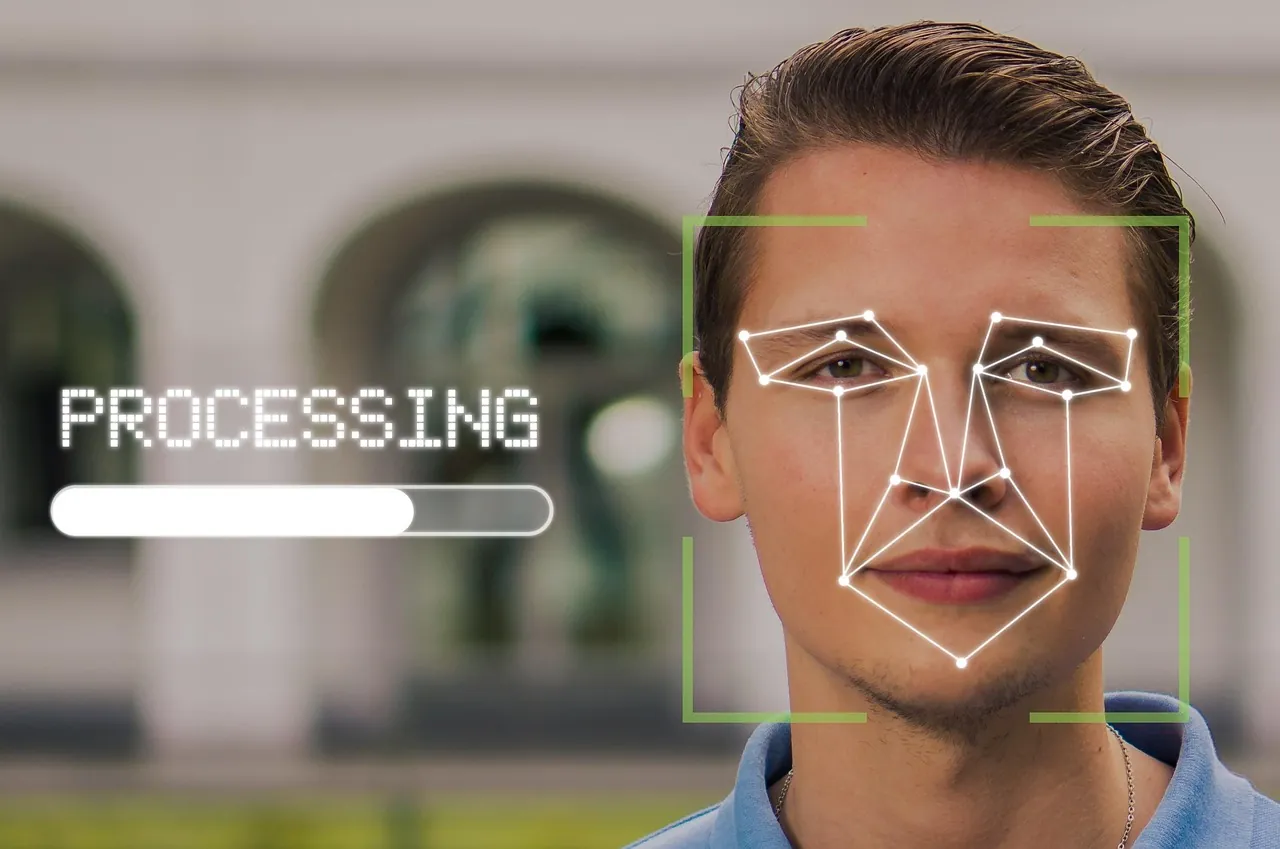
Assessing Risks When Merging Biometrics and Traditional Authentication Methods
Understanding the Hybrid Authentication Model As digital threats evolve, so too must our approaches to safeguarding sensitive information. A…
User Experiences: Comparing the Security of Password Managers and Old-Fashioned Storage
Understanding Password Storage Methods In the digital age, securing online accounts is paramount. With threats evolving constantly, the choi…

Effective Use of Password Managers to Mitigate Breach Risks
The Growing Importance of Password Managers In today's digital age, with data breaches becoming an all-too-common occurrence, safeguarding p…


