Section
Malware And Phishing
Guides, explainers, and practical reads updated regularly.
All Articles
Assessing the Impact of Technological Advances on Malware Delivery Methods
The Evolution of Malware Delivery in Phishing Attacks Phishing has long been a favored method for cybercriminals to deliver malware. However…
Step-by-Step Breakdown of Common Malware Utilizing Phishing Schemes
Understanding the Connection Between Phishing and Malware In the vast landscape of cybersecurity threats, phishing remains one of the most e…
Training Staff to Prevent Ransomware: A Case Study from Canada
The Rising Threat of Ransomware in Education Ransomware attacks have become a pervasive threat in the digital landscape, affecting various s…

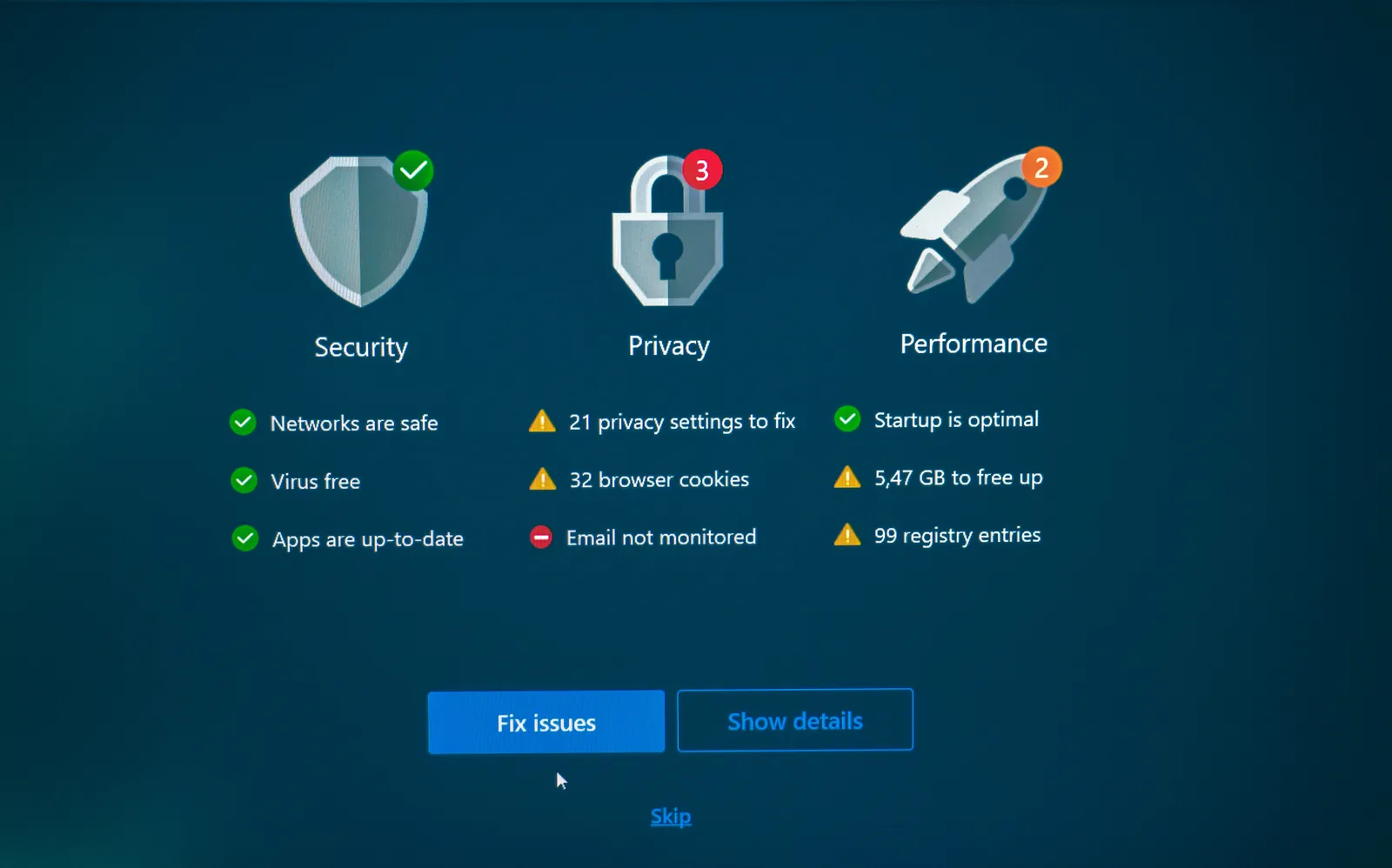
How to Spot Suspicious Links and Attachments in Emails
Recognizing the Anatomy of a Phishing Email Email remains a primary vector for cyber threats, particularly phishing attacks. Cybercriminals…

Analyzing the Impact of Phishing Training on Employee Behavior
Understanding the Need for Phishing Awareness Training Phishing attacks are a persistent threat to organizations worldwide. These deceptive…

Identifying Malware: Key Signs in Phishing Emails You Should Know
Understanding the Anatomy of a Phishing Email In the evolving landscape of cybersecurity threats, phishing emails remain a primary vector fo…

Ransomware Recovery: Steps Taken by a Healthcare Provider to Bounce Back
The Impact of a Ransomware Attack on Healthcare In late 2021, a prominent healthcare provider became the latest victim of a sophisticated ra…

Three-Step Verification Framework for Analyzing Suspicious Emails Safely
Understanding the Threat: Advanced Phishing Emails Phishing attacks have evolved significantly, transforming from blatant scams to sophistic…