identifying secure browsing indicators to protect sensitive work data

Understanding Secure Browsing Indicators
In today's digital age, protecting sensitive work data requires more than just strong passwords and regular software updates. Employees need to be vigilant when browsing the internet, especially when handling confidential information. This article will guide you through identifying secure browsing indicators to ensure that your online activities do not compromise sensitive work data.
Why Secure Browsing Matters
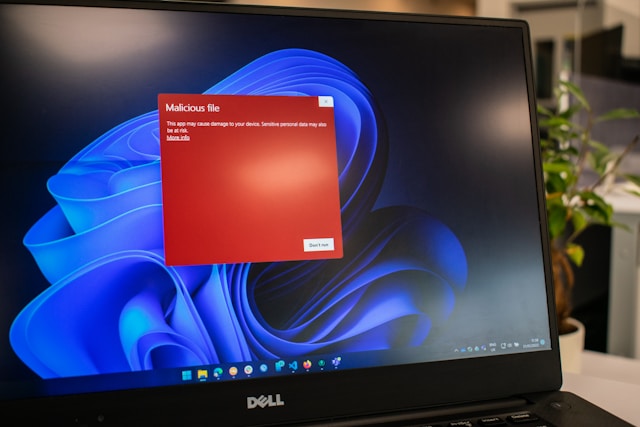
Secure browsing is crucial for preventing unauthorized access to sensitive data and protecting against cyber threats like phishing attacks, malware infections, and data breaches. For businesses, the consequences of a security lapse can be severe, including financial loss, legal issues, and damage to reputation.
Identifying Secure Websites
The first step in secure browsing is knowing how to identify whether a website is safe. Here are some key indicators:
- HTTPS Protocol: Look for 'https://' at the beginning of the URL. The 's' stands for secure, indicating that the website encrypts data transmitted between the server and your browser.
- Padlock Icon: A padlock icon in the address bar signifies a secure connection. Clicking on the icon usually provides certificate details, which can be inspected for validity.
- Valid Security Certificates: Check the certificate issuer to ensure it's from a trusted Certificate Authority (CA). Expired or untrusted certificates should raise a red flag.
Scenario: Accessing Confidential Client Data
Imagine you're working remotely and need to access client data stored on a cloud-based platform. Before entering any login credentials or downloading files, assess the website's security:
- Check for the HTTPS protocol and padlock icon in the URL bar.
- Click the padlock to view the security certificate details. Verify that it's issued by a reputable CA like DigiCert or Let's Encrypt.
- Ensure that your browser and antivirus software are up-to-date to avoid exploitation of known vulnerabilities.
By confirming these elements, you reduce the risk of exposure to malicious actors.
Implementing a Secure Browsing Checklist
A comprehensive checklist can help employees maintain secure browsing habits. This checklist includes practical steps for verifying website security before accessing or sharing sensitive information:
Checklist for Secure Browsing
- Verify Website Legitimacy: Always start by checking the URL. Typosquatting or spoofed websites often have URLs that are similar to legitimate sites but with slight variations.
- Inspect Email Links: If accessing a website from an email link, hover over the link to see its destination before clicking. Ensure it matches the expected domain.
- Avoid Public Wi-Fi for Sensitive Transactions: Use secure connections, such as a company VPN, when accessing sensitive information from outside the office.
- Use Security Plugins: Consider using browser extensions like HTTPS Everywhere or uBlock Origin to enhance security and block unwanted tracking scripts.
- Regularly Update Software: Keep browsers and plugins updated to patch known vulnerabilities. Set automatic updates where possible.
Scenario: Sharing Files via a Web Application
Your team uses a web application to share project files. Before uploading or downloading documents, apply the following steps:
- Ensure your browser shows a secure connection indicator (HTTPS and padlock).
- Verify that you're on the official web application site by cross-checking the URL against bookmarked links.
- Utilize two-factor authentication (2FA) if the service offers it, adding an extra layer of security beyond just a password.
These practices help mitigate risks associated with data interception during file transfers.
Conclusion
Developing secure browsing habits is essential for protecting sensitive work data in any organization. By being aware of key security indicators and following a structured checklist, employees can significantly reduce their vulnerability to cyber threats. Encouraging these practices across all levels of your organization strengthens overall cybersecurity posture and fosters a culture of vigilance.