Assessing Risks When Merging Biometrics and Traditional Authentication Methods
Understanding the Hybrid Authentication Model
As digital threats evolve, so too must our approaches to safeguarding sensitive information. A hybrid authentication model that combines biometrics with traditional passwords offers a promising solution by leveraging the strengths of both methods. While passwords can be stolen or guessed, biometrics provide an additional layer of security tied to unique physical attributes.
Combining these methods, however, is not without its risks. It is essential to carefully assess and manage these risks to maximize security benefits without compromising user convenience.
Why Combine Biometrics and Passwords?
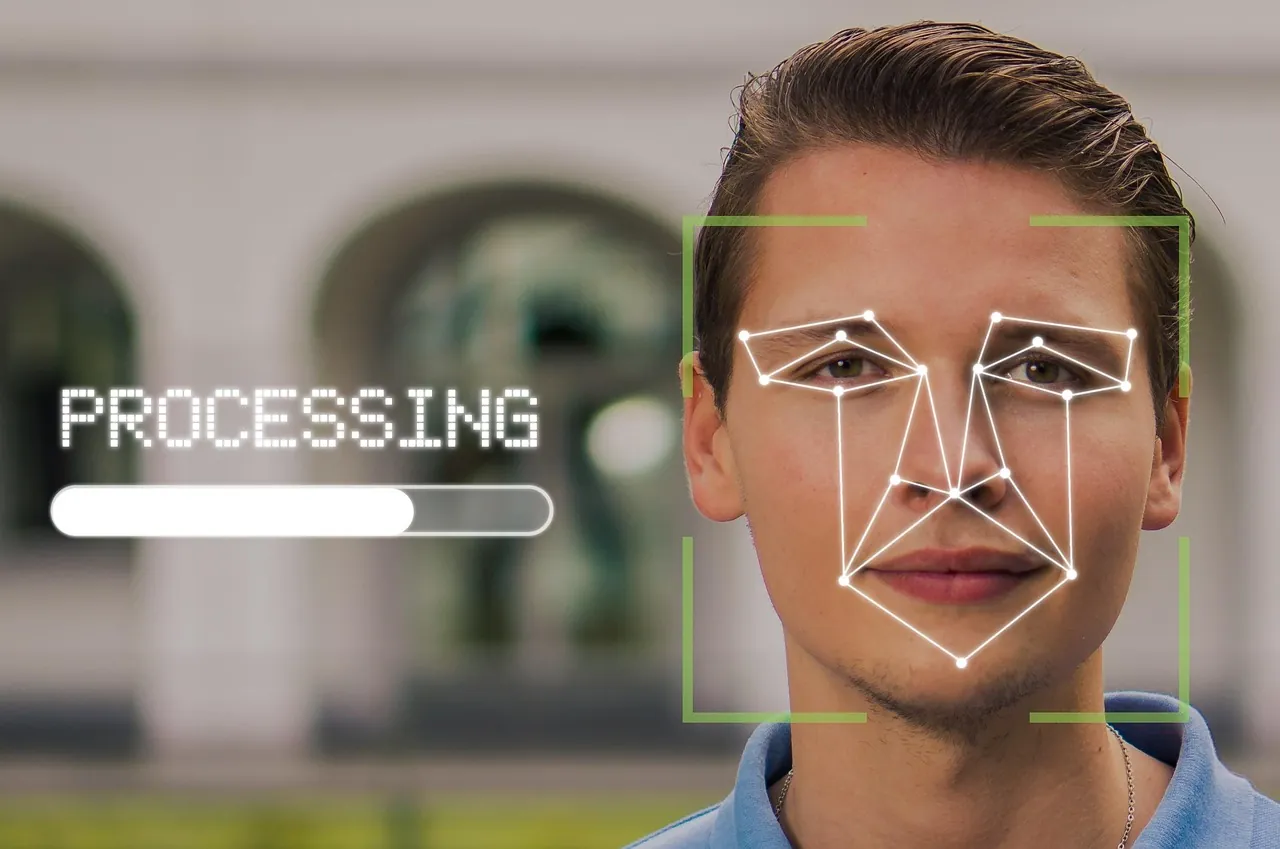
The primary advantage of combining biometrics with passwords is the enhancement of security through multifactor authentication (MFA). Traditional passwords are vulnerable to phishing attacks, brute force attempts, and social engineering. Biometrics, on the other hand, offer unique identifiers such as fingerprints, facial recognition, or iris scans that are harder to duplicate.
By requiring two forms of identification, the system ensures that even if one layer is compromised, unauthorized access is less likely. For example, a hacker might obtain a password but would still need the user's biometric data to proceed.
Assessing Risks in Hybrid Authentication
Before implementing a hybrid authentication model, organizations must conduct a thorough risk assessment to understand potential vulnerabilities and how to mitigate them effectively.
Identify Security Requirements
Begin by identifying the specific security requirements of your organization. Consider factors such as the type of data you are protecting, user accessibility needs, and compliance obligations under laws like GDPR or CCPA.
- Assess the sensitivity of data being protected.
- Determine the consequences of a potential breach.
- Evaluate user demographics and potential resistance to change.
Evaluate Biometric Options
Not all biometric methods are created equal. Choose biometric technologies based on your specific security needs and practical implementation considerations.
Fingerprints: Fingerprint scanners are common due to their accuracy and ease of use. However, they require careful management to avoid spoofing and can be less effective if users have certain physical conditions or injuries.
Facial Recognition: This method offers a hands-free experience, but it may struggle in low-light conditions or with individuals who wear accessories that alter their appearance significantly.
Iris Scans: Although highly accurate, iris scans require more expensive equipment and may raise privacy concerns among users due to the intrusiveness of capturing eye data.
Analyze Integration Challenges
Merging biometrics with traditional passwords involves technical challenges that must be carefully managed. These include compatibility with existing systems, integration costs, and ensuring seamless operation across all platforms.
- Ensure compatibility with current hardware and software systems.
- Calculate costs associated with new equipment and potential downtime during integration.
- Plan for ongoing maintenance and updates to biometric systems.
Selecting Appropriate Biometric Methods
Selecting the right biometric method involves balancing security needs with practicality. Considerations should include ease of use, accuracy, cost, and privacy implications.
User Experience Considerations
The usability of biometric systems is crucial for user acceptance. Systems that are difficult or cumbersome to use will face resistance and might lead to reduced security if users attempt to bypass them.
- Test different biometric systems with a sample group to gather feedback on usability.
- Ensure fast and reliable performance under various conditions.
Privacy Concerns
Biometric data is inherently sensitive, raising significant privacy concerns. Organizations must address these through clear policies and robust security measures.
- Implement strong encryption for stored biometric data.
- Clearly communicate how biometric data will be used and secured to gain user trust.
User Training and Awareness
The effectiveness of any authentication method depends heavily on user compliance and understanding. Comprehensive training programs are essential to educate users about the benefits and limitations of hybrid authentication models.
Developing Training Programs
Create targeted training programs focusing on the secure use of both passwords and biometric authentication. These should include:
- An introduction to why biometrics are being integrated into current systems.
- Tutorials on how to correctly use new biometric systems.
- Guidance on creating strong passwords that complement biometric authentication.
Monitoring and Feedback
Continuous improvement is vital in maintaining robust security. Solicit feedback from users regularly to identify issues and areas for improvement.
- Set up channels for users to report problems or concerns promptly.
- Regularly update training materials based on user feedback and technological advances.
A Case Study: Implementing Hybrid Authentication in Financial Services
A major financial institution recently undertook the task of integrating biometric authentication into their existing password-based systems. This case study highlights some key considerations and outcomes of their journey.
The Challenge
The institution faced an increase in cyber threats targeting customer accounts. They needed a more robust authentication method that wouldn't deter customers from using online services due to inconvenience or privacy concerns.
The Approach
The institution decided to implement fingerprint recognition alongside traditional passwords for their mobile banking app. This decision was made after evaluating several options and considering factors such as ease of use and cost-effectiveness. User workshops were conducted to gather insights into customer preferences and concerns regarding biometric data usage.
The Implementation
- The integration was rolled out gradually, beginning with pilot testing among a small group of users.
- User training sessions were organized both online and offline, ensuring broad access to guidance materials.
The Results
The introduction of fingerprint scanning led to a significant reduction in unauthorized access attempts while maintaining high customer satisfaction levels. Customers appreciated the balance between enhanced security and user-friendliness, which encouraged wider adoption of mobile banking services.
Conclusion: Balancing Security and Usability
The merging of biometrics with traditional authentication methods represents a strategic approach to enhancing security in an increasingly digital world. By conducting a comprehensive risk assessment, selecting appropriate technologies, and investing in user education, organizations can successfully deploy hybrid authentication systems that protect sensitive information while maintaining user convenience. As technology continues to evolve, staying ahead of potential threats requires ongoing evaluation and adaptation of security practices.






