Understanding the Role of Device Monitoring in Home Network Security

The Emerging Threat of IoT in Home Networks
The proliferation of Internet of Things (IoT) devices in our homes—from smart thermostats and security cameras to refrigerators and lighting systems—has transformed how we interact with our living spaces. However, these devices often serve as potential entry points for cyber threats, making home networks increasingly vulnerable.
Most IoT devices are designed to be convenient and easy to use, prioritizing rapid market release over robust security measures. This often leads to products with inadequate security features that become part of the sprawling attack surface hackers can exploit. For example, in 2016, the Mirai botnet attack highlighted how unsecured IoT devices could be used en masse to bring down major websites, underscoring the risks associated with poor device security.
Common Vulnerabilities Introduced by IoT Devices
Many IoT devices are compromised due to factors like weak default passwords, lack of regular software updates, and insufficient encryption protocols. A common vulnerability is the "default credentials" problem, where devices come pre-configured with factory-set usernames and passwords that are rarely changed by users.
For instance, many routers ship with generic credentials like "admin" and "password," which attackers can easily guess. Once they gain access, they can control the network or pivot to other connected devices. Regularly updating these settings is a fundamental step in securing your home network.
Strategies for Enhancing IoT Security
Network Segmentation
One effective strategy to mitigate risks is network segmentation, which involves dividing a network into multiple segments or subnetworks. This limits an attacker's ability to move laterally within your network should they compromise one device.
- Guest Network for IoT: Set up a separate guest network specifically for IoT devices. This ensures that even if an IoT device is compromised, the attacker cannot easily access your main network where personal computers and sensitive data are stored.
- VLAN Implementation: Utilize Virtual Local Area Networks (VLANs) to segment traffic logically without requiring physical separation. This approach is more suitable for tech-savvy users who want finer control over their network's flow of information.
Device Monitoring and Management
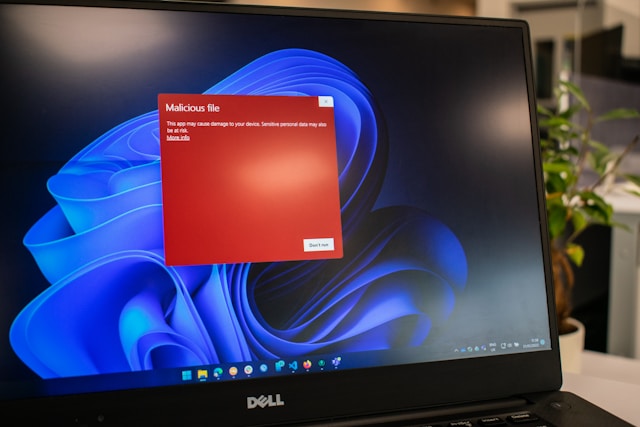
Device monitoring plays a critical role in identifying abnormal behaviors that could indicate a security breach. Implementing monitoring tools can help you track what devices are connecting to your network and what data they're transmitting.
- Use Network Monitoring Tools: Employ tools like Fing or PRTG Network Monitor to keep tabs on connected devices and monitor for unusual traffic patterns or new device connections.
- Regular Audits: Conduct routine audits of your device inventory. Keep a list of authorized devices and regularly check this against actual network activity to detect unauthorized additions.
A Case Study: Securing a Smart Home
Consider a real-world example of Jane, a homeowner who installed several IoT devices to automate her home. Initially, Jane did not change any default settings or segment her network. After attending a cybersecurity workshop, she became aware of the potential vulnerabilities in her system.
Jane decided to implement network segmentation by setting up a guest network exclusively for her IoT devices. She also began using a tool called Wireshark to analyze network traffic and identify unusual patterns. Within weeks, she detected an unauthorized attempt to access her smart thermostat and took swift action by isolating the device from her network until a security patch was applied.
Practical Tips for Home Network Security
- Change Default Passwords: Immediately change default passwords upon installation of any new device.
- Regular Software Updates: Ensure that all devices receive firmware updates regularly to protect against known vulnerabilities.
- Two-Factor Authentication (2FA): Enable 2FA wherever possible to add an extra layer of security.
Ultimately, maintaining security in a home network filled with IoT devices requires vigilance and proactive management. By implementing strategic measures such as network segmentation and diligent device monitoring, homeowners can significantly reduce their risk exposure and enjoy the convenience of their smart technologies without sacrificing safety.