Essential Elements of an Effective Malware Defense Plan for Small Businesses
Understanding the Threat Landscape
In the world of small business, understanding the threat landscape is the first step toward creating a robust malware defense plan. Malware, which includes viruses, ransomware, and spyware, poses a significant risk to businesses of all sizes. Unfortunately, small businesses often lack the resources and expertise to combat these threats effectively.
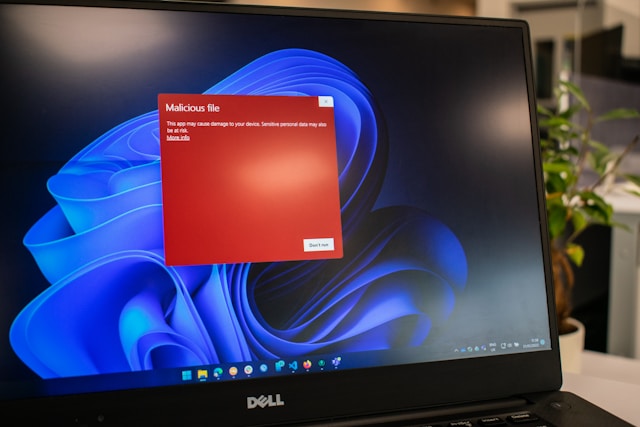
Malware can infiltrate your systems in numerous ways, such as through phishing emails, malicious websites, or compromised downloads. Once inside, it can steal sensitive data, lock you out of your systems, or cause other forms of disruption. To stay ahead, you must be proactive in identifying these threats and mitigating their risks.
Developing a Comprehensive Response Plan
Creating an effective malware response plan involves multiple steps:
1. Regular Backups
A solid backup strategy is critical. Implement automatic, scheduled backups of your business data to a secure location. This practice ensures that you can quickly restore your system in case of a ransomware attack or data corruption. Consider cloud-based solutions for offsite backups to provide an extra layer of security.
2. Employee Training
Your employees are your first line of defense against malware attacks. Conduct regular training sessions to educate them about phishing scams, safe browsing practices, and email protocols. Encourage a culture of security awareness where employees feel empowered to report suspicious activity.
3. Use of Antivirus and Anti-Malware Software
Invest in reliable antivirus and anti-malware software. These tools can detect and remove threats before they cause significant harm. Ensure that these programs are set to update automatically to protect against the latest threats.
Implementing Strong Security Policies
In addition to technical measures, implementing strong security policies is crucial. These policies serve as guidelines for secure operations within your organization.
Access Controls
Limit access to sensitive information based on employee roles. Not everyone needs access to every piece of company data. Implement role-based access control (RBAC) to ensure that employees have access only to the information necessary for their work.
Password Management
Enforce strong password policies that require regular updates and encourage the use of passphrases instead of simple passwords. Consider using password managers to store and encrypt passwords securely.
Email Security Protocols
Email is a common vector for malware attacks. Implement email filtering solutions to block spam and phishing attempts. Train employees on how to recognize phishing emails and encourage them to verify suspicious requests through direct communication channels rather than responding via email.
Monitoring and Incident Response
Even with the best prevention measures in place, incidents can still occur. A quick response can minimize damage significantly.
Network Monitoring
Implement network monitoring tools to detect unusual activity or potential intrusions. These tools can provide alerts in real-time, allowing you to respond swiftly to potential threats.
Incident Response Plan
Your incident response plan should outline the steps to take when a malware attack is detected. Assign roles and responsibilities ahead of time so that everyone knows what to do during an incident. Include steps for containment, eradication, and recovery.
Evaluating and Updating Your Defense Plan
The cybersecurity landscape is ever-changing, so it's important to regularly evaluate and update your defense plan.
Regular Audits
Conduct regular security audits to identify vulnerabilities in your current setup. Engage with cybersecurity professionals who can provide an external perspective and suggest improvements.
Feedback and Continuous Improvement
Create a feedback loop where employees can report issues or suggest improvements to security protocols. Use this feedback to make continuous adjustments and enhancements to your security measures.
A Practical Mini-Framework for Small Businesses
This mini-framework offers a structured approach small businesses can follow to enhance their malware defense:
- Assess: Identify key assets and evaluate potential threats.
- Implement: Deploy antivirus software, establish access controls, and configure automatic backups.
- Educate: Train employees on cybersecurity best practices and conduct regular refreshers.
- Monitor: Use network monitoring tools to detect anomalies early.
- Respond: Have an incident response plan ready, outlining specific actions for various scenarios.
This approach emphasizes continuous assessment and improvement, empowering small businesses to build a resilient defense against malware threats.






