Framework for Assessing the Best Identity Theft Apps Available

Understanding the Importance of Identity Theft Protection Apps
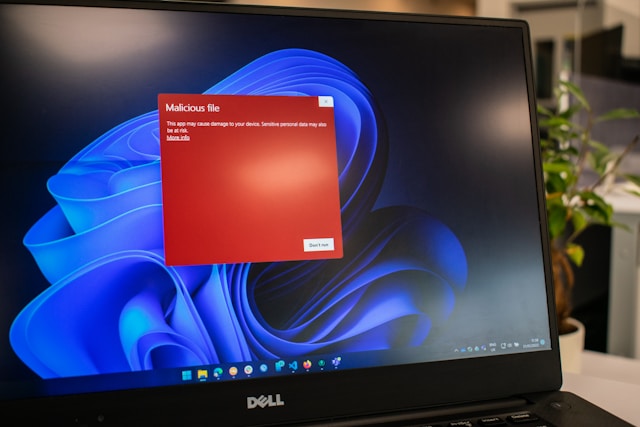
In today's digital landscape, the risk of identity theft has escalated significantly, prompting individuals to seek robust protection mechanisms. Identity theft protection applications have emerged as essential tools in this battle. They serve as digital guardians, monitoring and alerting users to potential threats.
The real challenge, however, lies in selecting an app that aligns with your specific needs while providing effective protection. This article presents a comprehensive framework for evaluating identity theft protection apps, ensuring you can make informed decisions.
Key Features to Look for in Identity Theft Protection Apps
A high-quality identity theft protection app should offer a range of features to ensure comprehensive coverage. Here are the key features to prioritize:
- Real-Time Monitoring: The app should continuously monitor your personal information across various databases and alert you to any suspicious activities.
- Credit Monitoring: Instant alerts on changes to your credit report or score can help identify unauthorized activity promptly.
- Dark Web Scanning: The app should search the dark web for your personal information, such as Social Security numbers and bank account details.
- Identity Restoration Services: Should you fall victim to identity theft, the app should offer comprehensive restoration services to help recover your identity.
- Insurance Coverage: Look for apps offering financial reimbursement for certain expenses incurred due to identity theft.
Evaluating Usability and User Experience
Beyond features, usability plays a critical role in the effectiveness of any app. A complex interface can deter users from utilizing all the available features, potentially compromising security. Consider the following aspects when evaluating usability:
- User Interface (UI): The design should be intuitive and easy to navigate, allowing users to access features quickly without requiring extensive technical knowledge.
- Customer Support: Reliable customer service is vital for addressing user queries or resolving issues promptly.
- Mobile Compatibility: Given the prevalence of mobile devices, ensure that the app offers a robust mobile version with full functionality.
A Practical Scenario: Evaluating Usability
Imagine a user named Sarah who has recently downloaded an identity theft protection app. The app boasts numerous features, but Sarah struggles to locate them due to a cluttered interface. Consequently, she misses crucial alerts about potential threats. This scenario underscores the importance of user-friendly design in ensuring optimal use and security.
Assessing App Effectiveness in Real-World Scenarios
An app's performance can only be truly assessed in real-world scenarios. Here are steps to evaluate an app's effectiveness practically:
- Conduct Simulated Attacks: Use test accounts to simulate data breaches or phishing attempts. Assess how effectively the app identifies and responds to these threats.
- Review Case Studies: Research documented cases where the app has successfully prevented or mitigated identity theft incidents.
A Real-World Example: Case Study Analysis
Consider a scenario where a financial institution deployed an identity theft protection app across its customer base. A case study revealed that within six months, the app prevented over 50 potential identity theft incidents through early detection of suspicious activities. Such tangible results are critical indicators of an app’s effectiveness in safeguarding identities.
Incorporating User Reviews and Ratings
User reviews provide invaluable insights into an app's performance from a consumer perspective. When assessing reviews, focus on:
- Common Complaints: Recurrent issues may indicate inherent flaws in the app.
- Praise for Specific Features: Positive feedback about particular functionalities can highlight areas where the app excels.
A Realistic Workflow: Analyzing User Feedback
Create a spreadsheet categorizing feedback into strengths and weaknesses. Look for patterns that can help inform your decision-making process. For example, if multiple reviews praise the app's dark web scanning capabilities but criticize its customer support, it highlights an area that may need additional consideration.
The Role of Security Certifications
Security certifications serve as a testament to an app's credibility and commitment to safeguarding user data. Key certifications to look for include:
- ISO/IEC 27001: This standard demonstrates adherence to international best practices for information security management systems (ISMS).
- SOC 2 Compliance: Ensures the app meets criteria for security, availability, processing integrity, confidentiality, and privacy.
A Practical Tip: Verifying Certifications
Visit the official website of certification bodies to verify an app's claimed certifications. Genuine certifications will often link back to these sites, confirming their authenticity.
Integrating Apps into Personal Security Practices
The final step in selecting an identity theft protection app is ensuring seamless integration with your existing security measures. Consider how well the app complements other tools like antivirus software or password managers you may already use. Here are some integration tips:
- Synchronization: Check if the app can sync data with your password manager or antivirus software, enhancing overall security coverage.
- Cross-Platform Accessibility: Ensure the app supports multiple devices you use daily, from PCs to smartphones.
A Scenario: Personal Integration Strategy
John uses both a password manager and antivirus software alongside his identity theft protection app. He ensures all systems are synchronized so alerts from one platform trigger responses across all others. This integrated approach enhances his defense against potential threats by creating a unified security front.
A Step-by-Step Checklist for App Evaluation
- Define Your Requirements: List out what you need most from an identity theft protection app (e.g., credit monitoring, dark web scanning).
- Research Features: Investigate which apps offer these features comprehensively.
- Evaluate Usability: Test the user interface and customer support quality.
- Assess Real-World Effectiveness: Review case studies and conduct simulated attacks where possible.
- Incorporate User Feedback: Analyze reviews focusing on repeated praises and complaints.
- Verify Security Certifications: Confirm certifications like ISO/IEC 27001 or SOC 2 compliance.
- Test Integration Capabilities: Check compatibility with other security tools and cross-device functionality.
This checklist serves as a practical guide to systematically evaluate identity theft protection apps, helping you make informed decisions tailored to your unique security needs.